Healthcare data unchained!
We often hear the aphorism, “Anything put on the internet, stays on the internet.” I suggest a corollary, “Anything put on a computer can be retrieved by a determined inquisitor.” So it is even for the most intimate of personally identifiable information – healthcare records. Given massive nationwide efforts to digitize our healthcare encounters, and given the frequency with which those digits are shared among insurers, contractors, researchers, public health officials, health information exchanges, pharmaceutical companies, healthcare providers, and the host of other interested parties who claim a legitimate interest, it is inevitable that data will go astray and be misused – illegally or inappropriately! It is said of computer hard-drives that one does not ask if a failure will occur, but when. I maintain that the same dictum holds true of personal health information. If computer-wielding crooks can steal from banks (which we assume use the highest degree of on-line and network protection), how impregnable is the healthcare industry? Apparently not so much.
Big data-hack at Anthem.
Earlier this month, health-insurer behemoth Anthem announced that the personal healthcare and credit card information of as many as 80 million of its customers may have been compromised. A secondary wave of attacks is already occurring as scammers send email warnings pretending to be from Anthem or credit-protection companies seeking to extract even more personal information from frightened Anthem customers. The Anthem breach strikes close to home. At last week’s UofL board of Trustees meeting, it was announced that some 5700 UofL employees might be on the Anthem list. I may be one of them. Not a good feeling. I feel violated enough when my personal healthcare information is being used to target me with marketing propaganda cloaked as important medical information. Having the same information in the hands of bona fide crooks gives me the willies.
Not the first major breach to be disclosed.
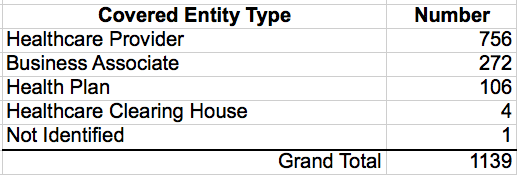
Although noteworthy for the size of the breach, its occurrence is hardly unique. As it happens, first the HITECH Act and then the Affordable Care Act requires that the Secretary of U.S. Health & Human Services must “post a list of breaches of unsecured protected health information affecting 500 or more individuals.” It has been referred to as “The Wall of Shame.” Even without quibbling over what constitutes a breach or parsing the several exceptions to reporting, that list is long and growing. It surely represents only the tip of the iceberg. The current list of reported breaches includes 1139 instances involving over 41 Million records– virtually all since 2008. One can only speculate how many smaller breaches have occurred or how many large breaches went unreported or unrecognized. The Anthem breach may almost double the number of compromised records already posted on this government “Wall of Shame.” A spreadsheet of the list is available online, or can be downloaded here. Some relevant observations I derive from the list include:
• Breaches have occurred in all states, DC, and Puerto Rico. The more populous the state, the more likely to have had a breach.
• Healthcare providers were the most frequent entities to have been breached, but business associates and health plans were well represented.
• Business associates of the record custodians were responsible for the largest number of individual records breached— 55%
• Seventy of the entities (6.7%) had more than one breach— 20 had more than 2 breaches.
• The list contains some of the most respected names in healthcare providers, hospitals, or insurers.
• Of the 1139 listed breaches, 206 had an additional note providing more details about the nature of the violation. In 1% of those, the data was being used for “research.”
• Multiple types of breach in a single episode often occurred, but roughly in descending order: Theft, Loss, Hacking/IT Incident, Improper Disposal, and Unauthorized Access/Disclosure were most common. The mode of breach was categorized as “Other” or “Unknown” in 99 instances (8.9%).
• By far, the most common source of compromised information was on desk- or laptop-computers, other physical electronic devices, electronic medical records, and network servers. Old-fashioned theft of paper or film records was also common.
How about in Kentucky?
Kentucky has not been spared from appearing on this list of major breaches. Attached is the list of 26 Kentucky entities extracted from the master list. That number seems compatible with our size. Compared to the rest of the country, we are over-represented for Healthcare Providers as the covered entity and Theft. We are underrepresented on Health Plans and Business Associates or on Hacking/IT Incident. We too have a few repeaters.
Is this the price of doing business?
Our healthcare system/industry is so fragmented, and its relevant functional components so widely distributed that information must correspondingly be broadly shared. Just getting various electronic medical record systems, billing systems, prescribing systems, or administrative systems able to talk to each other has proven impossible so far. To complicate matters, detailed health records can be accessed in a wide variety of ways including on provider’s cell phones or iPads – at home, in the office or hospital, or on the road. Detailed patient-specific information is routinely required by governmental entities, health plan operations, and (hopefully) in the past, even by employers. When the HIPPA medical privacy law was written, many exceptions to the privacy of patients were built in, including the ability of drug companies and researchers to peek at personal health records. In my opinion, our privacy structures more resemble a glass house than a bank vault.
Why do hackers want Anthem’s data?
No doubt there is more information in Anthem’s archives than just medical diagnoses. Items of great use to identity thieves form the core of medical information, including names, addresses, and phone numbers linked to social security numbers, credit card information, employers, family members, and all the other items we freely enter when we sign up at the front desk of our providers or in applications for insurance. Much more can be imputed such as socioeconomic status or family income. I suspect that the credit card and financial information will be of greatest immediate use to data thieves, but there will most probably be some attempt at blackmail over one medical diagnosis or another. More sophisticated misuse will occur as data thieves assemble contact lists of groups of patients to be sold to unscrupulous purveyors of quackery or worse.
How long will we tolerate our loss of privacy? Should we care?
As such breaches become more widely recognized, and as the skill of the thieves develops, eventually some major changes in the way we do our business will be demanded. If such changes require less fragmentation of our healthcare system, all the better. As we work our way through that process, I believe we need to also consider what are current legal, but in my opinion inappropriate uses of personal medical information. Drug companies and researchers should need my permission to peruse my medical records. Hospitals should be much limited in their use of third parties to cross-market things they want to sell. For example, I should not have received a letter from my hospital marketing a multi-item panel of screening tests that all reputable health professional organizations deem to be wasteful if not harmful. I should not have to wonder why I am getting mailings or emails trying to sell me things that apply to my personal health situation. Health Information Exchanges in which we are encouraged to enroll should not be allowed to package and sell my pharmaceutical history to drug companies for the personal profit of individuals claiming to represent the public health. As my readers might surmise, I am almost more offended by some of the “legal” misuses of my personal health information than I am by its possible theft! You can add many more of your own concerns to these lists, and I encourage you to do so. Remember, it is not if you will be injured by misuse of your personal information, but when.
Peter Hasselbacher, MD
President, KHPI
Emeritus Professor of Medicine, UofL
Feb 16, 2015

The day after I posted this article, I extended it with an analysis of the the reported breaches that exposed more than 100,000 individuals.
Peter